
Introduction: The New Face of Cyber Warfare
The rise of AI in cyber attacks has reshaped nearly every aspect of modern digital life — from automation and creativity to finance and security. However, in 2025, a new frontier of smart malware and AI-driven cyber threats is completely redefining cybersecurity as we know it.
In recent years, machine learning–powered attacks have evolved in real time, bypassing traditional defenses and targeting organizations of all sizes. Consequently, from small startups to government agencies, no entity is safe from intelligent, self-learning malware capable of adapting faster than most security teams can respond.
According to the IBM 2025 Cost of a Data Breach Report, companies using AI-enhanced threat detection tools reduced breach costs by 35% compared to those relying on legacy systems. Therefore, the message is clear — as attackers get smarter, defenders must evolve even faster.
At MentorShore, we prepare cybersecurity professionals and business leaders to anticipate, detect, and neutralize these next-generation threats. In this article, we explore how AI in cyber attacks is transforming digital defense — and what it means for your organization in 2025 and beyond.
Understanding AI-Driven Cyber Threats in 2025
What Makes AI Cyber Threats and Malware “Smart”?
To begin with, understanding AI-driven cyber threats is essential to staying ahead in today’s digital landscape. Unlike traditional malware, which follows predictable patterns, smart malware now leverages machine learning (ML) and neural networks to observe, learn, and evolve dynamically.
It continuously studies:
- System responses to previous attacks
- Security log patterns and anomalies
- User behavior such as login times and data access habits
Using this intelligence, AI malware can:
- Modify its behavior to blend with normal network traffic
- Mask its command-and-control signals
- Lay dormant until specific triggers appear
In other words, it’s not just an infection — it’s a thinking adversary.
Common Forms of AI-Powered Attacks
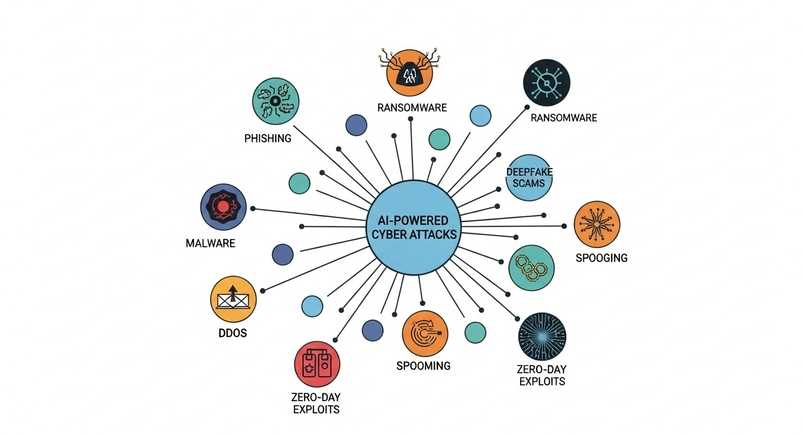
AI has supercharged traditional attack methods. Consequently, cybersecurity experts in 2025 are facing increasingly deceptive and complex threats. Below are the most prevalent forms:
Adaptive Phishing Campaigns
AI can scrape public data, social media activity, and even tone of voice from digital footprints to craft highly personalized phishing emails that mimic trusted contacts. Consequently, employees are more likely to click malicious links.
Polymorphic Ransomware
This self-altering malware changes its code or encryption patterns with every infection. Therefore, traditional antivirus tools struggle to recognize it effectively.
Deepfake Impersonation
Attackers now use AI-generated voice and video deepfakes to impersonate executives or partners, tricking employees into transferring funds or revealing credentials.
Autonomous Botnets
Self-governing networks of infected devices launch multi-vector attacks simultaneously, capable of making independent decisions without human command.
AI-Enhanced Credential Stuffing
Automated systems can predict and test password combinations based on user habits, drastically reducing brute-force attack time.
Why 2025 Marks a Turning Point for Cybersecurity

Moreover, 2025 represents a major turning point in the fight against cybercrime. While defenders are improving, attackers are automating faster than ever before. Consequently, cybersecurity has become a continuous AI-versus-AI race where adaptability determines survival.
1. Automation Arms Race
AI used to be the defender’s edge. Now, attackers employ the same technology for offensive automation — generating new malware variants faster than humans can react.
In essence, cybersecurity firms are in a constant race: AI vs AI — and the winner is determined by who learns faster.
2. Human Error Still Reigns Supreme
Despite technological sophistication, most breaches still originate from simple human mistakes: clicking malicious links, reusing passwords, or neglecting software updates.
Therefore, an effective defense must merge technology with human training — combining adaptive tools with continuous cybersecurity awareness programs.
3. Zero Trust Becomes Non-Negotiable
With threats adapting from within, Zero Trust Architecture (ZTA) is no longer optional. Every user, device, and application must be verified continuously, even those inside your network.
Learn how Zero Trust frameworks redefine internal security in our detailed guide, Zero Trust Architecture 2025.
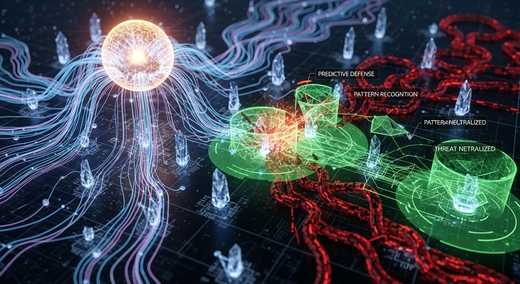
Detecting and Preventing AI-Powered Malware

In addition, detecting and preventing AI-powered malware requires a proactive, rather than reactive, approach. For example, behavioral analytics and anomaly detection now replace signature-based systems, allowing AI to catch unusual activity instantly.
Behavioral Analytics & Anomaly Detection
Rather than relying on traditional signature recognition, AI systems monitor baseline activity and flag deviations.
If a file requests unusual permissions or transmits abnormal data volumes, AI analytics can isolate the source within seconds — preventing damage before escalation.
Threat Intelligence Platforms
Advanced tools like CrowdStrike Falcon, Darktrace, and SentinelOne leverage global threat databases and predictive modeling to anticipate attacks before they occur.
Thus, these systems proactively flag potential malware variants — even those not yet documented — giving organizations the advantage of foresight.
Automated Incident Response
Once suspicious activity is detected, AI-powered orchestration tools can automatically:
- Isolate compromised devices
- Revoke access credentials
- Trigger forensic analysis
- Notify administrators
This automation reduces response time from hours to minutes — a crucial advantage during live cyber attacks.
Deception Technologies & Honeypots
Deception technologies deploy fake systems and data to trap hackers in simulated environments.
Every interaction reveals attacker behavior, helping analysts learn from real-time attacks while keeping core systems safe.
Therefore, this approach not only prevents breaches but also turns attacks into valuable intelligence opportunities.
Building a Strong AI Defense Strategy

Furthermore, building a resilient AI defense strategy demands multiple layers of protection. As a result, organizations that integrate predictive modeling, access control, and network segmentation enjoy far stronger resilience.
1. Strengthen Identity and Access Controls
- Enforce Multi-Factor Authentication (MFA) everywhere.
- Implement Role-Based Access Control (RBAC).
- Apply Just-In-Time (JIT) permissions to minimize exposure.
2. Upgrade Endpoint Protection
Traditional antivirus is obsolete. Adopt AI-based Endpoint Detection & Response (EDR) tools capable of detecting anomalies beyond known signatures.
3. Leverage Predictive AI Models
Deploy AI systems that understand your environment’s “normal.” When deviations appear — such as unusual login times or data transfers — the model can alert administrators instantly.
4. Network Microsegmentation
Divide your network into microzones to prevent lateral movement in case of a breach. Zero Trust segmentation ensures an attacker can’t move freely even after initial access.
5. Continuous Red Teaming & Cyber Drills
Human training remains crucial.
Conduct AI-driven phishing simulations, deepfake recognition workshops, and red-team exercises to test your organization’s readiness.
At MentorShore, we simulate real-world AI-powered attack scenarios to help cybersecurity teams build resilience through experience.
Case Study: When AI Malware Met Its Match

For instance, in mid-2025, a financial firm in Asia faced a self-learning malware that mutated every few hours. Thankfully, their AI-based behavioral detection spotted the anomaly early, allowing the team to neutralize it before major damage occurred
It detected encrypted traffic patterns shifting every 12 hours — a sign of self-mutating ransomware.
Here’s how they avoided disaster:
- Activated automated containment protocols
- Segmented their network with Zero Trust architecture
- Conducted emergency phishing simulations
- Reconfigured system privileges within 24 hours
The result: the malware was neutralized before encryption began, saving millions in potential damages.
Future of Cyber Defense: AI vs AI
By 2027, experts predict that over 80% of cyber campaigns will involve AI — whether for offense or defense.
Emerging technologies include:
- Self-healing systems that auto-repair infected code
- Predictive threat forecasting powered by neural networks
- Blockchain-secured identities for verified access control
Yet, technology alone won’t ensure safety. The human element — awareness, adaptability, and leadership — remains irreplaceable.
At MentorShore, we believe the strongest defense combines intelligent systems with intelligent people.
Conclusion: Staying Ahead of AI Cyber Threats in 2025

In conclusion, AI-driven cyber threats are no longer a distant concern — they are today’s reality. Therefore, every organization must combine smart technology with smarter training to stay safe in this new era.
Your organization’s best defense includes:
- AI & ML-based detection systems
- Zero Trust access control
- Endpoint and identity hardening
- Employee awareness programs
- Predictive modeling and continuous monitoring
At MentorShore, we empower individuals and organizations to stay ahead of these intelligent attacks through hands-on cybersecurity training and real-world AI threat analysis.
Enroll in our Cybersecurity Training Program and master the skills to defend against tomorrow’s AI-powered threats.
Stay vigilant. Stay adaptive. Stay secure.

